Commentary: Let me start by saying what this article isn’t.
This isn’t an article about Hillary Clinton (in fact, for the rest of the article, I’m simply going to talk about the “Secretary of State” or “Secretary”). This isn’t an article about records retention and access and possible motivations around that. And it’s not about questions of the law.
This article is about actions that we know the Secretary of State took, and what it means from the point of view of information security.
Information security is the most important point in this whole situation, in my opinion. And because of the usual political nonsense, it’s getting lost and we can’t afford for it to get lost: it relates directly to critical matters of national security.
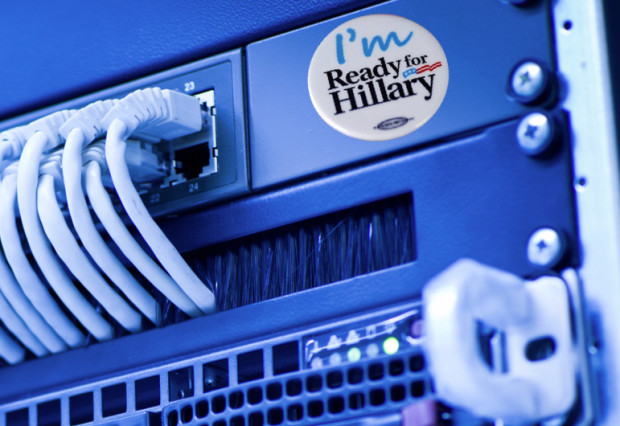
From this point of view, the facts are nearly undisputed. The Secretary of State did not use an email account that was hosted on an official State Department server. Instead, she used an email account on an outside server. All accounts indicate that this email account was used exclusively: the Secretary never used an official State Department email account hosted on State Department servers. And reports indicate that this email account was hosted on a physical server that was not physically under government control or protection. Some reports have even indicated that it was located in the Secretary’s personal residence. Some reports have characterized this as a “homebrew” server, and that’s apt and accurate.
These are the facts that we need to focus on from an information security point of view. Because if these facts are true, this can represent one of the most serious breaches in data handling that we’ve ever heard of.
This matters for three reasons.
- The Secretary of State is a very “high value target” from the standpoint of nation-state threat actors. The President, Secretary of Defense and the head of the CIA would also qualify in this top tier. These individuals handle the most important, most sensitive, most dangerous and therefore most interesting information to foreign intelligence.
- Nation-state threat actors represent the top of the food chain in terms of adversaries in information security. Nation-states can bring the most talent and resources to bear in this arena. For all the worry about cybercriminals and terrorists, everyone in information security looks at nation-state threat actors as the most advanced and sophisticated threat to defend against.
- Take #1 and #2 together and you have a situation where the very high value targets are threatened by the most advanced and sophisticated offensive information security capabilities out there. Put another way, the best of the best are gunning for those people to get their information.
The third point is critical: if the best of the best are after your information, you need the best of your best protecting it. And there is simply no way that a “homebrew” server is EVER going to have the security and resources appropriate to defend it adequately.
Looking at it this way, a “homebrew” server was the worst possible choice. Even using a webmail system like Gmail, Outlook or Yahoo would have been better because those companies have the expertise and capability to meet at least some of the threat this class of information would face.
This is the most important point. You can liken this to the CFO of Chase taking billions of dollars in cash home and storing it in the mattress. It’s so inadequate to meeting the risks that it would be laughable if it weren’t so serious.
Unless we learn that this server was being protected by the government using the same levels of protection that official servers are, we have no choice but to assume that this server has been compromised by foreign intelligence agents. And let’s be clear, this isn’t just hostile governments: if the Snowden disclosures have shown us anything (reminded us, really) it’s that everyone spies on everyone, friend and foe alike. To put this in the starkest terms: we have to assume the Russians, the Chinese, the Israelis have had access to the Secretary of State’s official email.
In any data breach like this, one of the questions we raise is whether this kind of action represents a failure of policy. Did the State Department have clear security policies and procedures that were communicated to its employees about the appropriate use of systems? This is important because it helps us understand if this is the failure of a single individual or if we have a bigger problem where others (including other Secretaries of State) could be creating the same kinds of risks.
RELATED POST
The press reports haven’t delved into this question adequately, being focused on other questions. I have the benefit of having a friend who was a political appointee to the State Department under a Secretary of State prior to the one in question. I asked this friend if there were clear guidelines that would make clear this was inappropriate, and I was told that everyone knew you only used your Blackberry for work, and only for work. Based on that, it would seem this was an intentional violation of security policies and procedures by this Secretary. The good news here, I suppose, is that we would seem to not have to worry that our ambassador to Russia is using Gmail or that John Kerry has his own server in his house.
But the fact remains that, unless we learn otherwise, this Secretary of State took actions that endangered the security of critical information in their trust and so the security of the United States. Regardless of one’s political affiliation and support that is a very serious violation, much more serious than the other violations being discussed.
What needs to happen is there needs to be a full investigation of the security piece of this. How secure was the server? Who was protecting it? Was there any evidence that it was compromised (though the best compromises are never detected)? Assuming that it was compromised, what information was on it and now has to be assumed to be lost?
But right now, the discussion isn’t focused on this. Where security is being raised it’s peripheral. These questions are secondary to other ones. And that is a problem.
This potentially could be the most serious national security data breach that we’ve heard of. The pieces are in place for it to be that. And part of the problem right now is we just don’t know and no one is focusing on those questions appropriately.
Hopefully calm heads will prevail and an appropriate investigation will occur so we can understand this situation better. But for now, I’m not hopeful that will happen. This critical piece of this situation may get lost in the shuffle as people focus on other, more interesting, but less important points.



